Sleeper Cells Meaning: The Hidden Threat Fully Explained

What if the most significant threats to national security aren’t the ones we see coming? Imagine a neighbor, a coworker, or a local business owner living an ordinary, unremarkable life for years, all while being a highly trained operative awaiting a single, coded signal to unleash a devastating attack. This scenario isn’t from a spy thriller; it’s the chilling reality of a sleeper cell. But what does this term actually mean?
This article provides a comprehensive look into the world of sleeper cells. We will explore a clear definition, trace their history from Cold War espionage to modern terrorism, and break down exactly how they operate. Crucially, we will also clarify the important distinction between a sleeper agent, whose primary goal is espionage, and a sleeper cell, which is fundamentally a tool of terrorism.
What is a Sleeper Cell? A Clear Definition
A sleeper cell is a covert group of terrorists who strategically embed themselves within a target country or community. They intentionally remain dormant, often for many years, building lives that appear entirely normal to avoid detection by law enforcement and intelligence agencies. Their members secure jobs, raise families, and participate in community life, creating a deep and convincing cover.
The core characteristics of a sleeper cell are its dormancy, its covert nature, and its reliance on an external trigger. Unlike active terrorist groups, they do not engage in criminal activity or communicate with their sponsors while dormant. They are activated only when a pre-arranged signal is given, at which point they execute a planned attack designed to cause mass disruption, psychological shock, and strategic damage.
“A sleeper cell basically means that someone has generally come into the United States whether legally or illegally and has set up a nefarious plot.”
— Former FBI Special Agent, as quoted by WPBF 25 News (2026)
Sleeper Cells vs. Lone Wolves: Understanding the Difference
The terms “sleeper cell” and “lone wolf” are often used interchangeably in media reports, but they describe fundamentally different threats. A sleeper cell is a coordinated group with external command, while a lone wolf acts entirely on their own. Understanding these differences is critical for threat assessment and counterterrorism efforts.
| Feature | Sleeper Cell | Lone Wolf Terrorist | Active Terrorist Cell |
|---|---|---|---|
| Structure | Small, coordinated group (2–10 members) | Single individual | Organized group with active command |
| Command | External command & control | Self-directed, inspired by ideology | Direct, ongoing contact with leadership |
| Activity | Dormant for years, then activated | Plans and acts alone | Continuously active in planning/operations |
| Detection | Extremely difficult due to inactivity | Very difficult, unpredictable | Easier to track via communications |
The Evolution of Sleeper Cells: From Cold War Spies to Modern Terror
The concept of the deep-cover operative has evolved significantly over the past century, shifting in both purpose and methodology.
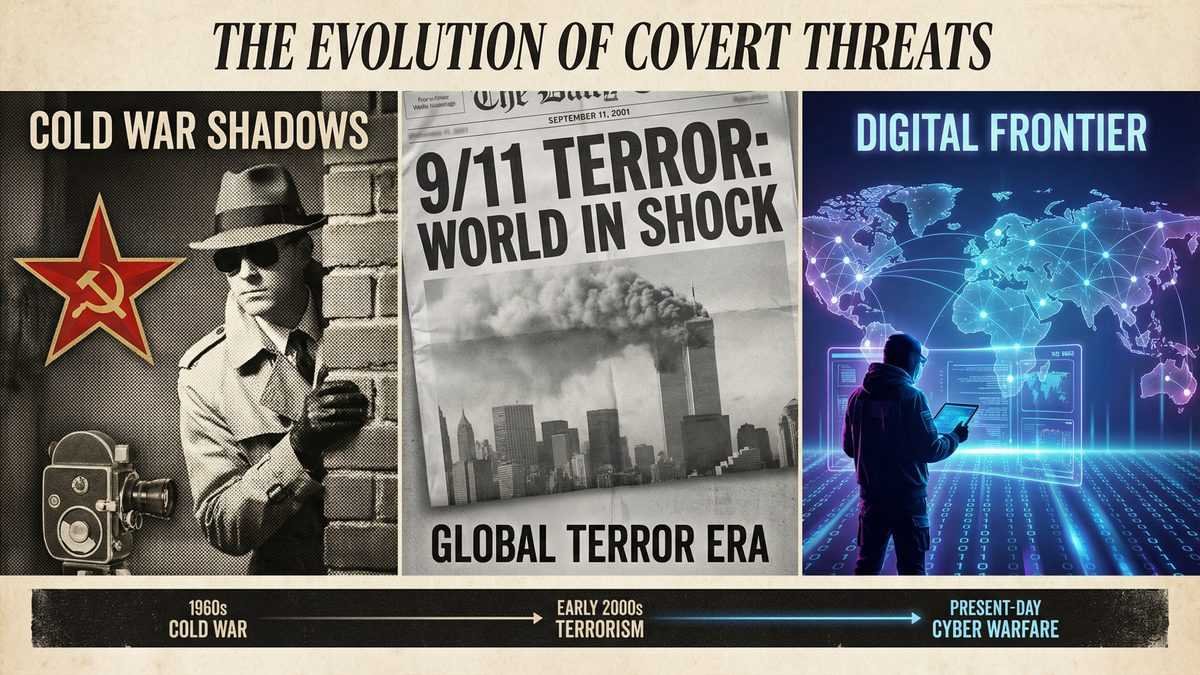
The Cold War Era (Espionage)
The Cold War was dominated by sleeper agents, individuals focused on espionage rather than terrorism. The Soviet KGB’s “Illegals Program,” for example, placed agents like Jack Barsky in the United States to gather intelligence and cultivate influence over decades. These agents were spies, not terrorists, tasked with stealing secrets, not taking lives. The infamous Cambridge Five spy ring in Britain serves as an early, potent example of how deep-cover agents could penetrate the highest levels of a nation’s government.
The Post-9/11 Era (Jihadist Terrorism)
The September 11, 2001 attacks marked a pivotal shift. The perpetrators were members of the Hamburg Cell, an al-Qaeda sleeper cell based in Germany. Led by Mohamed Atta, these men used their status as university students to live and plan for years, completely undetected. Their goal was not espionage but mass-casualty terrorism on a symbolic and catastrophic scale, forever changing the world’s understanding of the sleeper cell threat.
The Modern Era (State-Sponsored Proxies)
Today, the threat has morphed again with the rise of state-sponsored proxy violence. Nations like Iran and Russia are accused of using sleeper cells and agents not just for traditional spying but as tools for destabilization, political intimidation, and carrying out attacks through proxy forces. This modern form blurs the lines between intelligence operations and acts of war, creating a complex and dangerous new security landscape.
The Lifecycle of a Sleeper Cell: How They Operate
The operation of a sleeper cell follows a patient, multi-stage lifecycle designed to maximize secrecy and effectiveness.
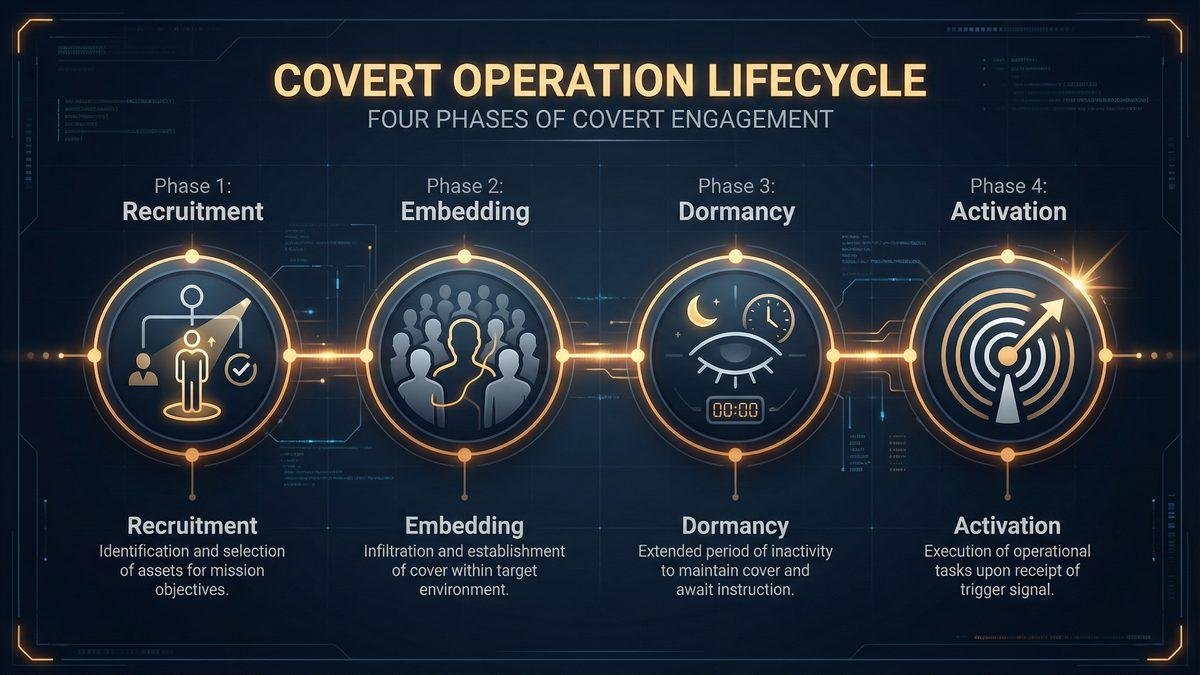
Phase 1: Recruitment & Indoctrination. Individuals are typically identified and radicalized in their home countries or in extremist hotspots abroad. They are chosen for their ability to blend in, their ideological commitment, and their patience.
Phase 2: Infiltration & Embedding. Operatives enter the target country, often legally through student or work visas. They then begin the long process of building a cover story, securing legitimate employment, establishing social networks, and integrating seamlessly into the community.
Phase 3: Dormancy & Low-Level Planning. This is the longest and most critical phase. The cell remains completely dormant, avoiding any activity that could draw attention. Communication with their sponsoring organization is minimal to nonexistent. During this time, they slowly and patiently gather information and make logistical preparations for their future mission.
Phase 4: Activation & Execution. Years may pass before the cell receives its activation order. This signal can come through a variety of means, such as a coded message, a courier, or a seemingly innocuous public broadcast. Once activated, the cell moves quickly to finalize its plan and execute the attack.
Real-World Examples: Three Infamous Cases
History provides several stark examples of sleeper cells and agents in action, each highlighting a different facet of the threat.
- The Hamburg Cell (Al-Qaeda): The architects of the 9/11 attacks, led by Mohamed Atta, lived as students in Hamburg, Germany. They leveraged the freedoms of a Western society to meticulously plan the deadliest terrorist attack in history, demonstrating the devastating potential of a patient, well-organized jihadist sleeper cell.
- The “Illegals Program” (Russia): Uncovered by the FBI in 2010, this ring of ten deep-cover Russian agents, including the now-famous Anna Chapman, had spent years living in American suburbs. Their mission was long-term influence and intelligence gathering, a classic example of state-sponsored espionage using sleeper agent tactics.
- The Lackawanna Six (Al-Qaeda): This group of six Yemeni-American friends from Lackawanna, New York, traveled to an al-Qaeda training camp in Afghanistan in 2001. Their subsequent arrest and prosecution highlighted the challenge of homegrown radicalization and the difficulty of intercepting a cell before it can be activated.
How Are Sleeper Cells Detected and Countered?
Countering a threat designed to be invisible is one of the greatest challenges for intelligence agencies. Because they remain dormant, sleeper cells leave very few traces for authorities to follow. Detection relies on a multi-layered approach that combines sophisticated technology with traditional human intelligence.
First and foremost, Human Intelligence (HUMINT) is often the most effective tool. Intelligence agencies work tirelessly to recruit informants and infiltrate extremist groups to learn about potential operatives before they are deployed. An inside source can provide the critical breakthrough that technology alone cannot.
Next, Signals Intelligence (SIGINT) involves monitoring vast amounts of global communications. While difficult, analysts search for the faint signals of activation or planning that might betray a cell’s existence. This is a painstaking process of finding a needle in a global haystack of data.
Financial Tracking provides another avenue. Following the money from state sponsors or terrorist financiers can sometimes lead to the discovery of a cell’s support network, exposing the logistical and financial underpinnings of a future plot.
Finally, International Cooperation is non-negotiable. No single country can fight this threat alone. Sharing intelligence between allied agencies like the FBI, CIA, MI6, and Mossad is essential to connecting the dots of a global conspiracy.
The public also plays a vital role. The U.S. Department of Homeland Security’s “If You See Something, Say Something®” campaign empowers ordinary citizens to report suspicious activity, providing tips that can be the crucial first thread in unraveling a plot.
Frequently Asked Questions (FAQ)
What is a sleeper cell in simple terms?
It is a small group of hidden terrorists who live normal lives in a community until they are “activated” to carry out an attack.
How do sleeper cells get activated?
Activation can happen through various secret methods, including a coded phrase in a broadcast, an encrypted email, or a message delivered by a courier.
What’s the difference between a sleeper agent and a sleeper cell?
A sleeper agent is typically a lone spy working for a government to steal information (espionage). A sleeper cell is a group of terrorists planning a violent attack.
Are there active sleeper cells in the U.S. today?
Intelligence officials operate under the assumption that they exist. FBI Director Christopher Wray has repeatedly warned of the persistent and elevated threat from foreign terrorist organizations and their operatives.
How long can a sleeper cell stay dormant?
They can remain dormant for many years, even decades. The members of Russia’s “Illegals Program” were embedded in the U.S. for over a decade before being discovered.
What was the most famous sleeper cell in history?
The Hamburg Cell, responsible for planning and carrying out the 9/11 attacks, is arguably the most infamous and impactful sleeper cell in modern history.
Do movies portray sleeper cells accurately?
While often dramatized, movies like The Manchurian Candidate or shows like The Americans capture the core concept of deep-cover operatives. However, the reality is often less glamorous and involves years of patient, mundane integration.
What should you do if you suspect terrorist activity?
Authorities urge the public to report any suspicious behavior to their local FBI field office or local police. You can also submit a tip directly at fbi.gov/tips. It is always better to report a concern than to stay silent.
Conclusion
The sleeper cell represents one of the most insidious and challenging threats in the modern world. It is a patient, calculated, and deeply hidden tactic that has evolved from the spy games of the Cold War to the global terrorism of the 21st century. While the actors and ideologies change—from KGB spies to al-Qaeda terrorists and state-sponsored proxies—the underlying strategy of using dormant operatives remains a persistent danger.
Understanding this threat is the first and most critical step toward countering it. In a world where the lines between peace and conflict are increasingly blurred, informed vigilance from both intelligence agencies and the public is our most powerful defense against the threats hiding in plain sight.
Sources: Merriam-Webster Dictionary; The 9/11 Commission Report (2004); FBI — Operation Ghost Stories (2011); NPR — The Lackawanna Six (2011); U.S. Department of Homeland Security — If You See Something, Say Something® campaign; Wikipedia — Hamburg Cell; Wikipedia — Sleeper Agent.
Last modified: March 10, 2026

